API Security Best Practices: Complete Guide for Secure APIs (2026)
nderstanding API security best practices is essential for protecting modern applications. APIs handle sensitive data, transactions, and system integrations, making them a major target for cyber threats.
In India and globally, fintech, banking, and digital platforms rely heavily on APIs. Following proper API security best practices ensures data protection, prevents fraud, and builds user trust.
Why API Security is Important
APIs are exposed endpoints that can be accessed over the internet. Without proper security, they can be vulnerable to:
- Data breaches
- Unauthorized access
- Injection attacks
- Denial-of-service attacks
https://owasp.org/www-project-api-security/
https://www.rfc-editor.org/rfc/rfc7231
Common API Security Risks
Broken Authentication
Weak authentication can allow unauthorized users to access APIs.
Data Exposure
Sensitive data may be exposed due to improper validation or encryption.
Injection Attacks
Malicious inputs can exploit vulnerabilities.
Lack of Rate Limiting
Unlimited requests can lead to abuse or system overload.
Misconfigured Security
Improper settings can expose endpoints.
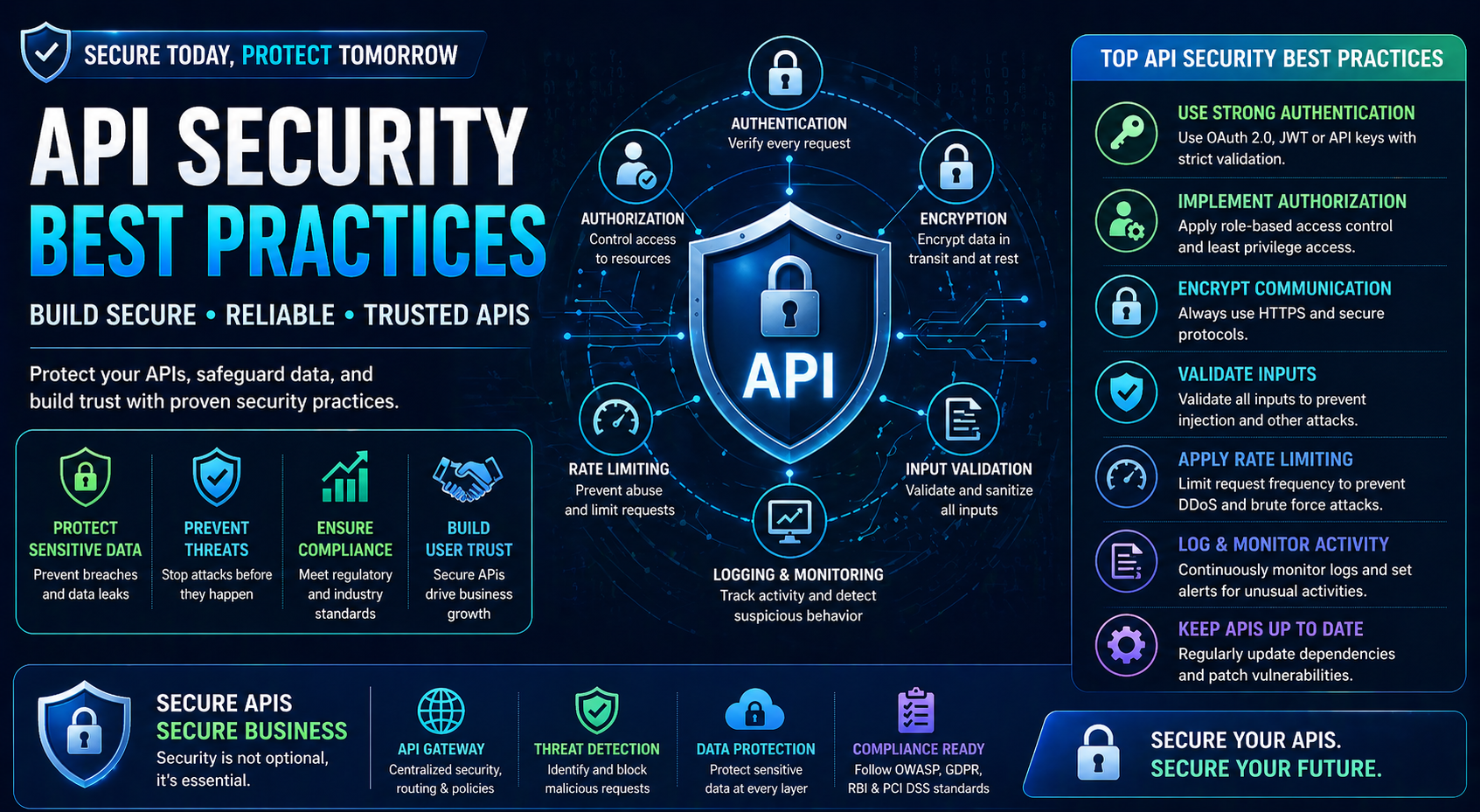
API Security Best Practices
Use Strong Authentication
Implement secure authentication methods such as:
- OAuth 2.0
- JWT (JSON Web Tokens)
- API keys with restrictions
Always verify user identity before granting access.
Implement Authorization Controls
Ensure users can only access permitted resources.
Use:
- Role-based access control (RBAC)
- Permission-based systems
Encrypt Data
Always use HTTPS for secure communication.
Encrypt:
- Data in transit
- Sensitive data at rest
Validate Input Data
Validate all incoming data to prevent:
- Injection attacks
- Malicious payloads
Use:
- Input sanitization
- Schema validation
Use Rate Limiting
Limit the number of API requests to prevent abuse.
Benefits:
- Prevent DDoS attacks
- Control traffic
- Protect system resources
Implement Logging and Monitoring
Track:
- API requests
- Errors
- Suspicious activity
Monitoring helps detect security issues early.
Use API Gateways
API gateways provide:
- Authentication
- Rate limiting
- Traffic management
- Security filtering
Secure API Endpoints
Do not expose unnecessary endpoints.
Ensure:
- Proper access control
- Hidden internal APIs
Token Expiration and Rotation
Tokens should expire after a certain time.
Use:
- Short-lived tokens
- Refresh tokens
- Key rotation
Protect Against Replay Attacks
Use:
- Nonces
- Timestamps
- Secure tokens
Use CORS Properly
Configure Cross-Origin Resource Sharing (CORS) correctly to avoid unauthorized access from external domains.
API Security in Fintech
Fintech APIs require stronger security due to financial data handling.
Examples:
- Payment APIs
- Banking APIs
- Money transfer APIs
https://nxtbanking.com/dmt-api
https://nxtbanking.com/bbps-api
Security Testing for APIs
Penetration Testing
Simulate attacks to find vulnerabilities.
Vulnerability Scanning
Identify weaknesses automatically.
Load Testing
Check system behavior under high traffic.
Security Audits
Review system configurations and code.
Tools for API Security
OWASP ZAP
Security testing tool.
Burp Suite
Used for penetration testing.
Postman
Testing APIs with authentication.
API Gateway Tools
Used for managing and securing APIs.
Common Mistakes to Avoid
Exposing API Keys
Never store keys in frontend code.
Ignoring HTTPS
Always use secure protocols.
Weak Password Policies
Use strong authentication rules.
Lack of Monitoring
Always monitor API usage.
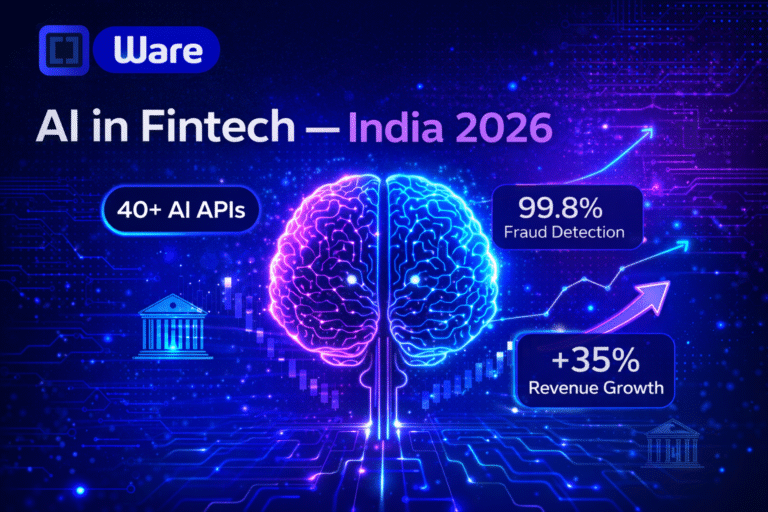
Future of API Security
The future includes:
- AI-based threat detection
- Zero trust architecture
- Advanced encryption
- Automated security monitoring
Conclusion
Following API security best practices is essential for building secure and reliable applications. APIs are critical components of modern systems, and securing them protects both businesses and users.
By implementing strong authentication, encryption, monitoring, and secure design, organizations can safeguard their APIs against threats and ensure long-term success.
https://nxtbanking.com/contact
About This Topic
The NxtBanking blog is India's authoritative technical resource for fintech API integration — covering Payout API, BBPS, AEPS, UPI, KYC, DMT, recharge APIs, and enterprise payment infrastructure. Every article is written by practitioners who have built and scaled payment systems processing millions of transactions, combining technical accuracy with real-world implementation guidance for developers, product teams, and fintech founders.
Quick Answers
What makes a good fintech API integration?
A well-built fintech API integration covers: proper OAuth 2.0 authentication, idempotency keys on every write request, webhook HMAC signature verification, exponential-backoff retry logic for transient errors, and a status-query fallback for ambiguous outcomes. NxtBanking's sandbox environment lets you test all these scenarios before production.
How do I handle failed transactions in a payment API?
Categorise failures: (1) Hard failures (invalid account, KYC mismatch) — do not retry; notify user. (2) Transient failures (timeout, 5xx) — retry with idempotency key and exponential back-off. (3) Ambiguous (no response) — call the transaction status endpoint before retrying to avoid duplicate processing.
Is NxtBanking RBI-compliant for payment APIs?
Yes. NxtBanking operates through RBI-licensed partner banks for all payment services (IMPS, NEFT, RTGS, UPI) and is NPCI-certified for BBPS, AEPS, and UPI flows. All APIs follow RBI's Master Directions on payment aggregators, KYC, and PMLA obligations. We maintain audit logs, data localisation, and consent frameworks compliant with the DPDP Act 2023.
How does NxtBanking handle API downtime and failover?
NxtBanking uses a connected-banking architecture that links a single API credential to multiple RBI-licensed partner banks. When one bank's rails experience degradation or maintenance, the API automatically routes to the next available bank — with no code change required on the client side. This multi-bank failover is what delivers 99%+ transaction success rates and 99.9% API uptime SLA for enterprise clients.
What does it cost to integrate NxtBanking APIs?
NxtBanking offers pay-as-you-go pricing with no setup fees and no minimum commitment for most APIs. Typical pricing: IMPS/UPI payout ₹3–₹8 per transaction, NEFT ₹1–₹3, BBPS bill payment ₹0.50–₹3, AEPS cash withdrawal ₹2–₹5. Enterprise clients on committed volumes negotiate flat-rate pricing. Sandbox access is free and unlimited. Contact sales for a custom quote based on your expected transaction volume.
Key Terms
- API
- Application Programming Interface — a structured software interface that lets applications communicate with each other over the internet using defined endpoints, authentication, and data formats.
NxtBanking is India's AI-powered fintech API platform trusted by hundreds of fintechs, BC networks, NBFCs, and enterprise companies. Our unified API marketplace covers payout (IMPS, NEFT, RTGS, UPI), BBPS bill payment with 20,000+ billers, AEPS biometric banking, KYC and identity verification (Aadhaar, PAN, Bank, Driving Licence, Voter ID, RC), UPI collection and QR codes, domestic money transfer (DMT), mobile and DTH recharge, Micro-ATM, and travel APIs — all under one master agreement, one set of credentials, and one consolidated monthly invoice.
Every NxtBanking API is backed by a 99.9% uptime SLA, real-time webhook delivery, a full-featured sandbox environment with simulated error scenarios, comprehensive API documentation with Postman collections and code samples in multiple languages, and dedicated technical onboarding support. Production go-live for most APIs is achievable within 7–15 business days after KYC and compliance review. For enterprise clients requiring custom SLAs, dedicated infrastructure, or white-label platform builds, NxtBanking offers tailored commercial terms with no minimum volume commitment at the pilot stage.