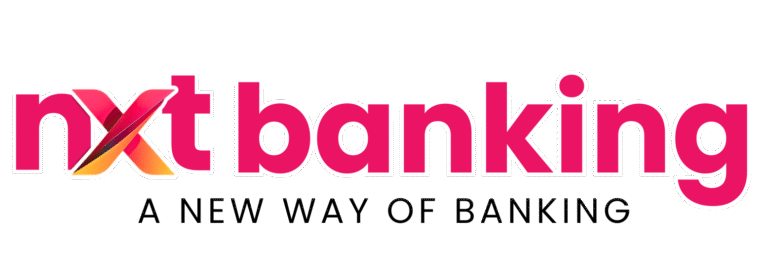
Security Measures in DMT API Integration: Complete Guide for Businesses (2026)
Understanding the right security measures in DMT API integration is essential for any business that wants to offer safe and reliable domestic money transfer services. Since DMT platforms handle sensitive financial data, user identity details, and transaction requests, security must be treated as a core requirement from the beginning.
A weak integration can lead to unauthorized access, duplicate transactions, data leaks, fraud attempts, and customer trust issues. That is why businesses and developers must implement strong security measures in DMT API integration before going live.
Inbound Link:
https://nxtbanking.com/dmt-api
Why Security Matters in DMT API Integration
DMT API integration connects your application with banking and payment infrastructure. This means your platform may process:
- Sender details
- Beneficiary account details
- Transaction amounts
- API credentials
- Reference IDs
- Status updates
- Callback responses
If these areas are not protected properly, even a small weakness can create serious operational and financial risk.
Core Security Measures in DMT API Integration
Strong Authentication
Authentication is the first layer of protection in any DMT system. Only authorized systems and users should be able to access API services.
Common methods include:
- API keys
- Client ID and secret
- Token-based authentication
- IP whitelisting
- Signature-based validation
API credentials should always be stored securely on the server side and never exposed in frontend code.
Outbound Links:
https://www.rbi.org.in/
https://www.npci.org.in/
Role-Based Access Control
Not every user or staff member should have access to all system functions. Role-based access control limits what each person can see or do.
Examples:
- Admin can manage settings and reports
- Support staff can view transactions but not change system credentials
- Finance team can access reconciliation data only
This reduces internal misuse and accidental errors.
HTTPS and Transport Encryption
All communication between your app, backend, and DMT provider should happen through HTTPS. Encrypted transport protects sensitive data from being intercepted during transmission.
Without proper encryption, data such as account numbers, transaction references, or tokens can be exposed to attackers.
Secure Credential Storage
API keys, secrets, and tokens should not be stored in application code or public files. They should be stored using secure methods such as:
- Environment variables
- Encrypted secret managers
- Restricted server configuration
Only the backend should access these credentials.
Input Validation and Sanitization
A strong part of security measures in DMT API integration is validating every request before it reaches the provider.
You should validate:
- Mobile numbers
- Account numbers
- IFSC codes
- Amount values
- Sender ID
- Beneficiary ID
- Transaction reference IDs
This helps prevent invalid requests, manipulation attempts, and injection-based attacks.
Unique Transaction References
Every transaction should use a unique reference ID. This helps prevent duplicate processing and makes status tracking easier.
Unique IDs are important for:
- Duplicate transaction prevention
- Reconciliation
- Fraud monitoring
- Callback matching
- Audit logs
Idempotency and Retry Protection
Sometimes users retry transactions when they do not receive an immediate response. If your backend is not designed carefully, this can create duplicate transfers.
To reduce this risk:
- Use unique request IDs
- Block duplicate submissions for the same transaction
- Apply retry rules carefully
- Recheck existing transaction status before reprocessing
This is one of the most important security measures in DMT API integration.
User-Level Security Measures
OTP Verification
OTP verification helps confirm user identity during registration, login, or important actions like beneficiary addition and money transfer.
OTP can be used for:
- Login verification
- Sender registration
- Sensitive account changes
- High-value transaction approval
This reduces unauthorized access risk.
KYC Verification
A secure DMT platform should use proper KYC processes to validate users before allowing money transfer services.
KYC helps with:
- Identity verification
- Fraud reduction
- Regulatory alignment
- Transaction limit control
Proper KYC is not just operationally useful; it is also part of secure system design.
Outbound Link:
https://uidai.gov.in/
Session Management
If user sessions are not handled securely, attackers may hijack access and misuse the platform.
Good session security includes:
- Session expiry rules
- Re-authentication for sensitive actions
- Logout from inactive sessions
- Secure token storage
Transaction Security Measures
Beneficiary Verification
Before sending funds, the platform should verify beneficiary bank details. This reduces transfer failure and prevents sending money to incorrect accounts.
Verification should confirm:
- Account number format
- IFSC validity
- Beneficiary existence if supported
- Matching transfer rules
Transaction Amount Controls
Your system should apply limits and checks before allowing transfer requests.
Examples include:
- Daily transfer limit
- Per transaction limit
- Sender category based limit
- KYC status based limit
These rules reduce fraud risk and support better compliance.
Real-Time Status Checks
Some transactions may return pending first and final status later. Real-time status checks help prevent confusion and reduce disputes.
A secure flow should:
- Store initial response
- Poll status when necessary
- Update final result only after confirmation
- Match callback and status data properly
Callback and Webhook Validation
If your provider sends callbacks, your server must verify that the callback is genuine before updating the transaction status.
Secure webhook handling should include:
- Source verification
- Signature or token validation
- Request logging
- Replay protection
- Safe parsing of payloads
Weak callback handling can lead to fake updates or incorrect transaction states.
Backend Security Measures
API Rate Limiting
To protect your DMT platform from abuse, you should limit how frequently requests can be sent.
Rate limiting helps prevent:
- Brute force attempts
- API abuse
- Automated fraud
- Denial-of-service patterns
This is especially important for login, OTP, sender verification, and transfer endpoints.
Server-Side Logging
Logging is one of the most practical security measures in DMT API integration. Logs help identify unusual activity, failed requests, fraud attempts, and system issues.
Important logs include:
- Authentication attempts
- Sender registration requests
- Beneficiary actions
- Transfer requests
- Callback payloads
- Status checks
- Failed validations
Logs should be protected and reviewed regularly.
Audit Trails
Audit trails provide a record of who did what and when. This is useful for compliance, support, and fraud investigation.
Audit trails should track:
- Admin actions
- User activity
- Credential changes
- Transaction updates
- Manual overrides
- Settlement adjustments
Database Security
Sensitive data in the database should be protected with access control and encryption where appropriate.
Best practices include:
- Restrict direct access
- Use strong database credentials
- Encrypt sensitive fields where required
- Separate environments for test and live systems
- Maintain regular backups
Fraud Prevention Measures
Risk Scoring and Suspicious Activity Detection
A mature DMT system should identify unusual patterns such as:
- Too many failed attempts
- Sudden high-value transfers
- Rapid multiple transfers
- Repeated beneficiary changes
- Multiple requests from unusual IPs
These patterns can be flagged for review or blocked automatically.
Device and IP Monitoring
Tracking login source, device behavior, and IP changes can help detect suspicious activity.
For example:
- New device login alerts
- Unusual location patterns
- Repeated login failures from same IP
- Multiple account actions from a shared source
Velocity Checks
Velocity checks limit how often a user can perform a sensitive action in a short time.
Examples:
- OTP requests per hour
- Beneficiary additions per day
- Transfer requests per minute
- Failed login attempts
These controls reduce abuse and fraud attempts.
Security Best Practices for Developers
Keep Sandbox and Live Separate
Never mix production credentials with test credentials. Sandbox and live environments should remain fully separated.
Do Not Trust Frontend Validation Alone
All critical checks must also happen on the backend. Frontend validation improves user experience, but backend validation provides real protection.
Use Secure Error Handling
Do not expose internal server details or API secrets in error messages. Show simple messages to users and keep detailed logs internally.
Patch and Update Dependencies
Frameworks, packages, and server components should be updated regularly to reduce known vulnerabilities.
Test Edge Cases
Developers should test for:
- Duplicate transfer attempts
- Expired tokens
- Invalid callback payloads
- Unauthorized access attempts
- Tampered request values
- Broken session flows
These tests strengthen real-world security.
Inbound Link:
https://nxtbanking.com/blog/dmt-api-integration-guide-for-developers
Common Security Mistakes in DMT API Integration
Hardcoding Credentials
Keeping secrets directly in source code is a major risk.
Weak Access Controls
Giving all staff full access increases internal risk.
Poor Logging
Without proper logs, fraud detection and troubleshooting become difficult.
Missing Duplicate Request Protection
This can lead to repeated transfers and customer disputes.
Insecure Callback Handling
Updating status without validating callback authenticity creates a serious vulnerability.
No Monitoring of Failed Attempts
Repeated failed logins, OTP abuse, or invalid requests may go unnoticed if not monitored.
Compliance and Regulatory Considerations
Security is closely linked with regulatory expectations. Businesses should ensure that their DMT operations support:
- KYC verification
- User authentication
- Data protection
- Transaction monitoring
- Audit records
- Reconciliation controls
A secure system is not just good practice; it also supports long-term operational trust.
Benefits of Strong Security Measures in DMT API Integration
When businesses implement proper security measures in DMT API integration, they gain several benefits:
- Higher customer trust
- Lower fraud risk
- Better transaction reliability
- Reduced support issues
- Easier reconciliation
- Stronger platform reputation
Security directly supports growth in fintech businesses.
Inbound Links:
https://nxtbanking.com/aeps-api-provider
https://nxtbanking.com/bbps-api
https://nxtbanking.com/contact
FAQs
What are the most important security measures in DMT API integration
The most important measures include strong authentication, HTTPS encryption, secure credential storage, input validation, duplicate request prevention, and secure callback handling.
Why is OTP important in DMT systems
OTP helps verify user identity and reduces the risk of unauthorized access or sensitive account changes.
How can developers prevent duplicate money transfer requests
Developers can use unique transaction IDs, idempotent request handling, backend checks, and careful retry rules.
Is HTTPS enough for DMT API security
No, HTTPS is important, but it must be combined with authentication, access control, validation, logging, and fraud prevention controls.
Conclusion
Implementing the right security measures in DMT API integration is essential for building a safe and reliable money transfer platform. Security should cover every layer of the system, including authentication, user access, request validation, transaction handling, callback verification, and fraud monitoring.
Businesses that take security seriously are better positioned to protect users, reduce losses, and build long-term trust. In a financial system where every transaction matters, strong security is not optional. It is a core part of success.
Inbound Link:
https://nxtbanking.com/dmt-api